The Secret Files description was changed some time ago. Previously it stated that secrets were accessible from /etc/secrets at runtime. Now it states:
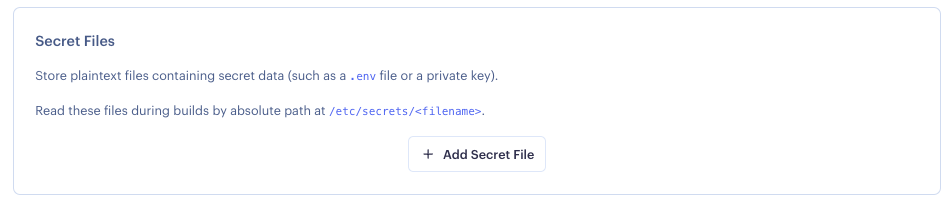
Secret Files
Store plaintext files containing secret data (such as a
.envfile or a private key).Read these files during builds and at runtime from your app’s specified root directory, or from the absolute path
/etc/secrets/<filename>.
I attempted to leverage this, as it’s much easier when .NET appsettings.json files are located in the application root directory. Currently we need to run sh -c ln -s /etc/secrets/appsettings.json && ./my-executable to start our program.
However when I removed the symlink command, it stopped working. I SSH-ed into the machine, and found that the secrets really are only in /etc/secrets. Why was the documentation changed, but the behaviour was not changed, and secrets really are only in /etc/secrets?
UPDATE: Nevermind, I guess it makes sense that this would only work if we built the docker container on Render. Ours is pulled from dockerhub. I guess in that case it only mounts the /etc/secrets. I guess the statement is just a bit too broad, which lead to this confusion.
I thought that the changed documentation meant render would pull the image from dockerhub, then add a layer on top that adds the secret files to the WORKDIR.